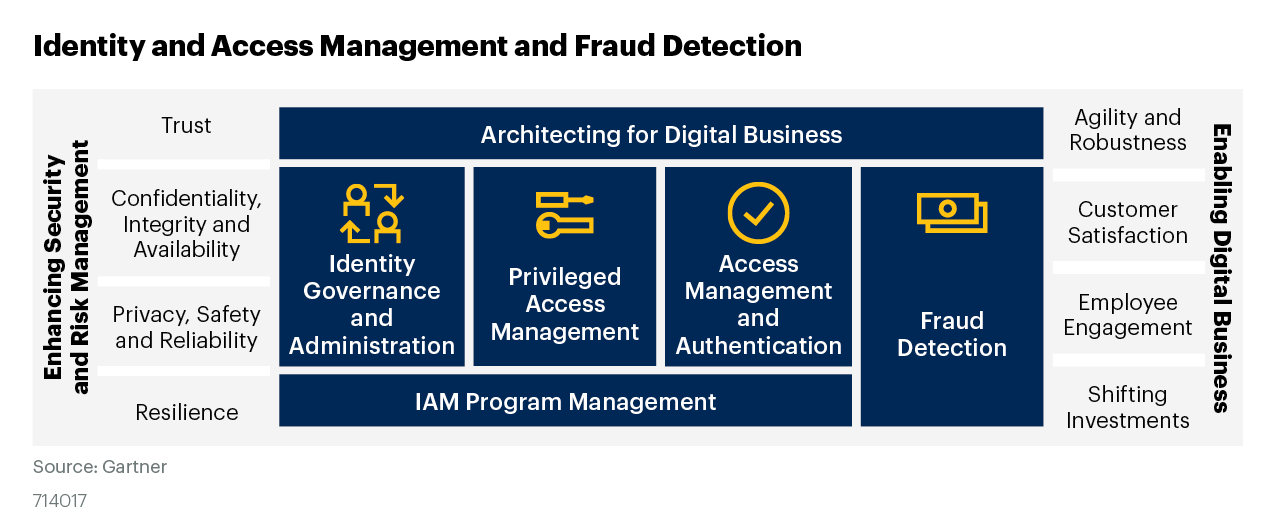
The pandemic has triggered a wave of identity and access management (IAM) challenges as businesses internally restructure, onboard specialized skillsets or face financial pressures to make redundancies. Industries experiencing huge demand have an incentive to expedite onboarding processes for new joiners, while others are doing the same for specialist skillsets they desperately need.
Globally, customers have realized that identity and access management has become the new perimeter security to ensure consistent security across their on-premise, hybrid cloud, and public cloud deployments of database, applications, and other workloads. Similar to their workloads, customers expect to deploy and manage their Identity and access platform solutions anywhere. The scale and types (e.g. IOT and Bots) of our digital economy are increasing the entities accessing enterprise resources, which is driving the need for identity solutions where identity life cycle and governance work together with intelligent access management to provide comprehensive security. Oracle’s Identity suite can address nearly any deployment use case. How to leverage?
Oracle IAM solutions secure access to enterprise applications for both cloud and on-premises deployments. Organizations can enable a Zero Trust strategy and establish user identity as a new security perimeter
Oracle Identity and Access Management (IAM) Products
- Oracle Identity and Cloud Service
- Oracle Cloud Infrastructure Identity and Access Management
- Oracle Access Management
- Oracle Identity Governance
- Oracle Directory Services
Let us deep dive into Oracle Identity and Cloud Service
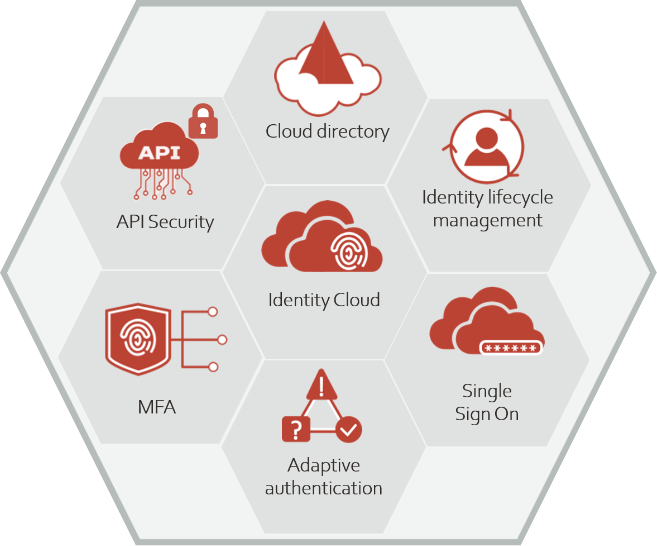
Oracle Identity and Cloud Service (IDCS)
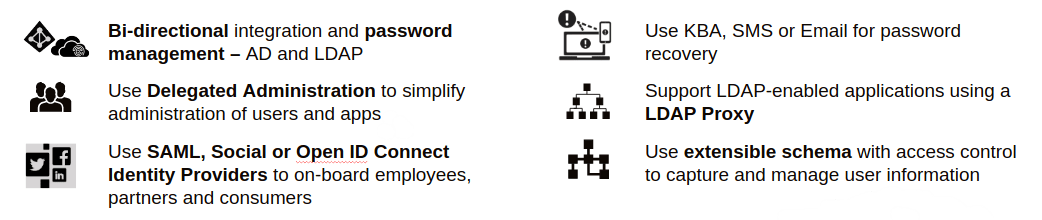
IDCS refer to Oracle Identity Cloud Service and it’s considered as Identity-as-a-Service (IDaaS) solution, Oracle Identity Cloud Service provides identity management, single-sign-on (SSO) and identity governance for applications on-premise, in the cloud and mobile applications. Any user can access the application at anytime, anywhere on a device in a secure manner. Oracle IDCS integrates directly with existing directories and identity management system, making it easier for users to access applications. Providing a platform that is robust and secure, allows users to access, develop and deploy their applications.
Components of Oracle Identity Cloud Service (IDCS)
Cloud Directory
A extensible, highly scalable repository to store information about users, groups, devices and application accounts
Key Features
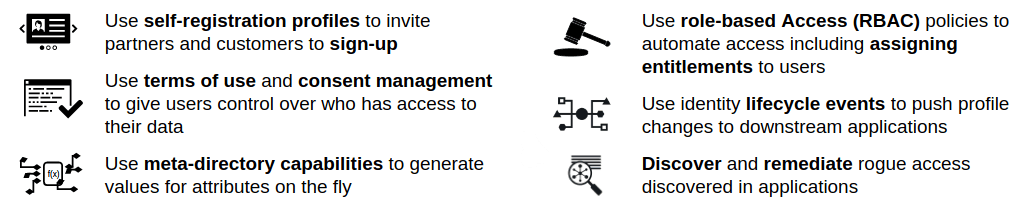
Identity Lifecycle Management
On-board employee, consumer and partner identities from any source and manage their lifecycle
Key Features
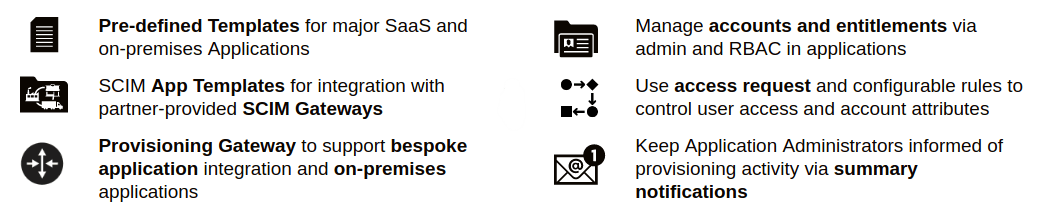
Identity Provisioning
Automates identity lifecycle processes & helps provision identities and their authorizations to cloud or on-premise
Key Features
Provisioning Gateway
- Supports all major enterprise applications ranging from Databases, Mainframes to SaaS applications
- Over 400 SaaS applications supported via Partner Gateways
- Almost any app can be integrated using SCIM
- Custom App Integration supported via custom connectors
- Highly available and cross-platform
- Can be deployed on-premises or in the Cloud (for Cloud-based workloads)
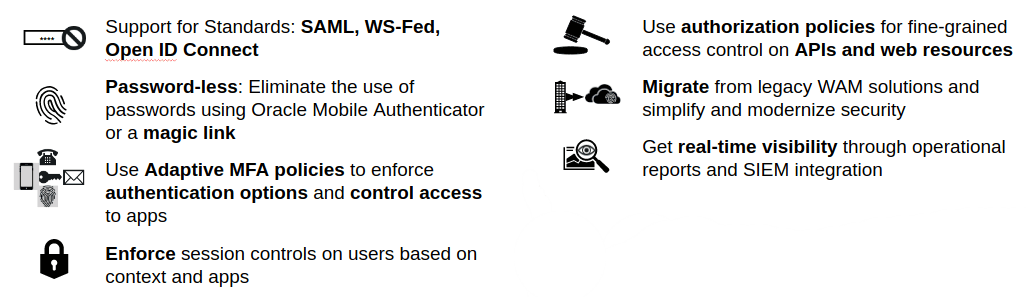
Single Sign-On
Enable employees, customers, and partners to access their applications seamlessly using a single authentication
Key Features
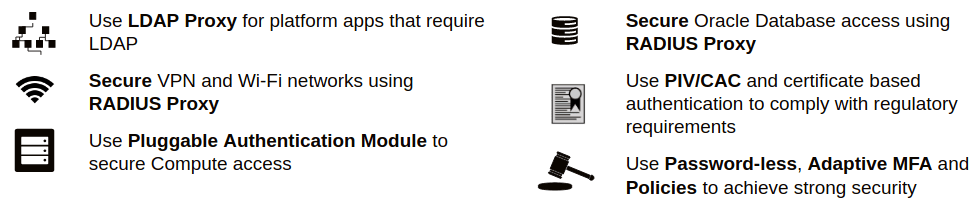
Platform Security
Secure access of privileged users in Databases, VPN, Wi-Fi and Compute
Key Features
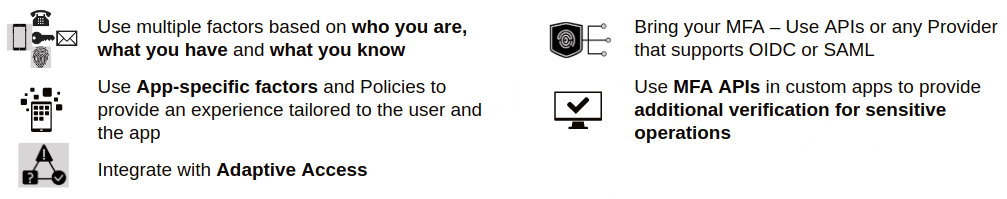
MFA
Secure access to apps and prevent credential theft
Key Features
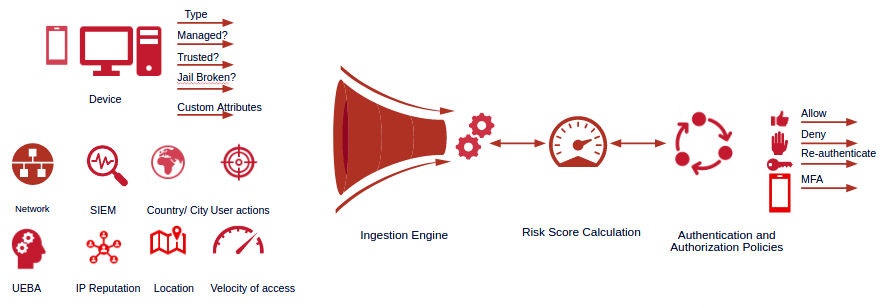
Adaptive Authentication
Add an additional layer of security by learning from the user’s behavior, context and external threat feeds
Key Features
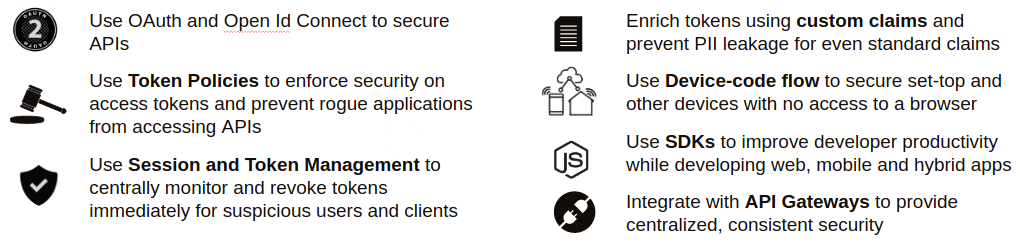
API Security
Standards-based, policy-driven centralized access management for APIs
Key Features